Connecting computer peripherals such as keyboard & mouse to a PC introduces potential data leakage and hacking risks. Black Box Secure KVM Switch line provides port isolation between networks ensuring no data is leaked between secure ports and the outside world. Built with true data path isolation between systems and networks, these switches help prevent hardware tampering.
Black Box offers a wide range of NIAP PSD V3.0 certified Secure KVM devices and PSD V.4.0 compliant models. Learn more about the NIAP Protection Profile and when you should shift to PP V4.0.

Access multiple computers assured that your data is protected from accidental or unauthorized transfer when switching between systems.

Securely control computers with port to port isolation for secure switching with no port crosstalk.

Achieve air-gap isolation between computing devices with data path isolation, preventing cyber hacking and data leakage in environments where security is critical.

Block peripheral exploits, data breaches, eavesdropping, and computer malware.

Protect from hardware and firmware tampering by enforcing multilayered security mechanisms.

Computers can be catalysts for malicious attack or intellectual property theft. Protect desktop access since your computer or device is a potential point of entry into your network.
Secure KVM Switches comply with NIAP PP V.3.0 security certification, equipping them with the high security features that still meet many of today’s Information Assurance safe control standards. We are proud to announce that NIAP has certified our new range of Secure KVM Switches under the latest NIAP PSD V.4.0 protection profile. These new Secure KVM Switches were among the first that became available with the NIAP PSD V.4.0 certification, meeting the latest cybersecurity requirements from Government.

Control multiple computers through a single keyboard, mouse, and up to four video displays while air-gap maintains absolute isolation between all connected systems.
Black Box offers a wide range of NIAP 3.0 certified Secure KVM Switches suitable for any type of application. Choose from KVM switch models with up to 16-ports, analog or digital video, single, dual or quad monitors.
Monitor systems with the highest analog or digital resolutions of up to 4K Ultra-HD 3840×2160 @ 30Hz.
Securely transfer files between computers and safeguard your network from accidental transfer, unauthorized access, or compromise of critical data.
Benefit from hardware-based peripheral isolation with no dependency on firmware, keyboard buffering, or memory.
Prevent unwanted and unsecure data to be transmitted through the DDC lines by means of secure EDID learning and emulation. The Secure KVM Switches are designed to learn the connected monitor’s EDID upon power up, allowing trouble-free connection to most monitors.
A fully advanced and configurable CAC port supports smart cards or biometric readers. Furthermore, authenticated admins can register and assign specific peripheral devices to the CAC port, allowing users to switch this device along with the KVM switching of the connected computers.
| Threat: | Solution: |
|---|---|
| Microprocessor malfunction or unanticipated software bugs causing data to flow between ports. | Unidirectional data flow is enforced by hardware "data diodes" so data isolation doesn't rely on software integrity. |
| Malicious modification of microprocessor software causing data to leak between ports. | Microprocessors are one-time programmable and soldered on the board. Data isolation does not rely on software; it is ensured by hardware. |
| Detection of signals on one computer by monitoring for crosstalk (leakage) signals on another computer. | No connections to sensitive inputs such as computer microphone ports. Minimum crosstalk separation provided between signals from one computer and input or I/O signals to another. |
| Timing analysis attacks (looking at what happens on one port to determine data flow patterns on another). | Only one computer is connected at a time to any shared circuitry. Links are unidirectional, preventing timing analysis. |
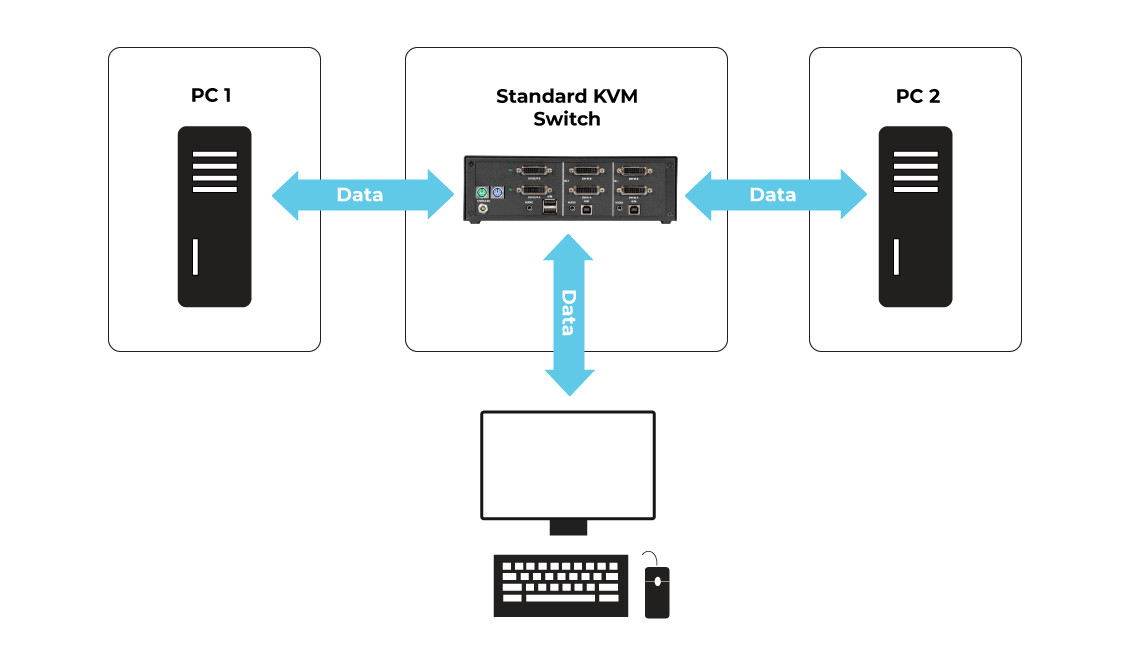
NIAP 3.0 certified Secure KVM Switches enable users to switch between unclassified networks as needed from a single keyboard and mouse, while isolating classified networks. Standard switching allows users access to public networks as required, protecting confidential data from accidental or unauthorized transfer.
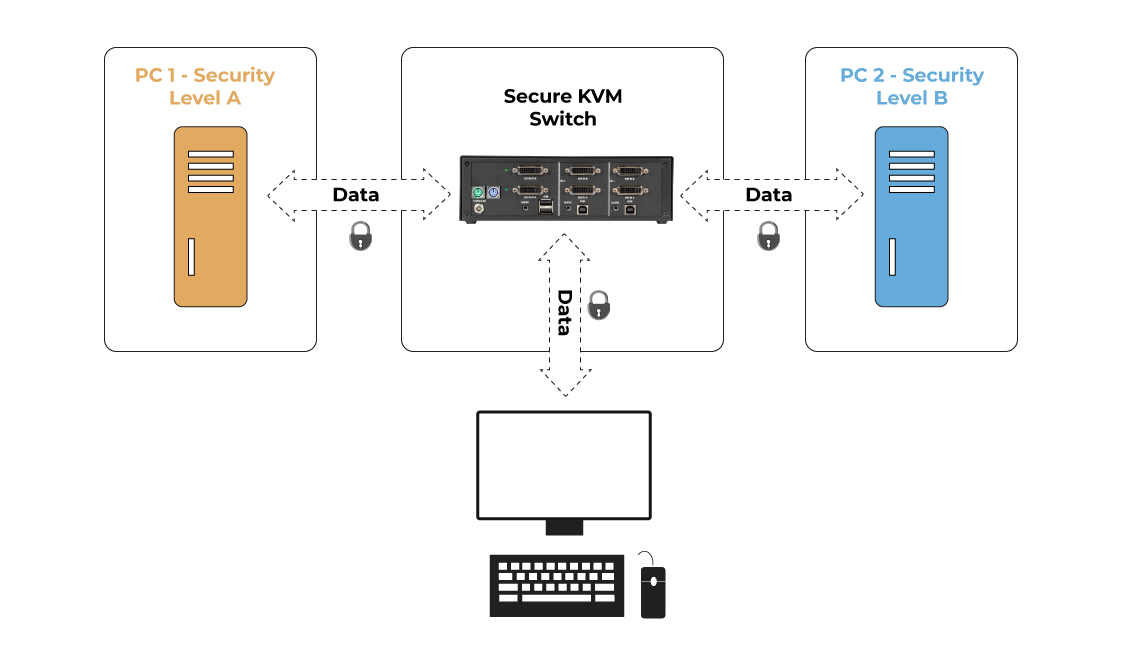
NIAP 3.0 certified Secure KVM Switches provide absolute isolation between networks, ideal for use in defense, intelligence, and other applications where sensitive data must be protected by controlling access to classified networks in addition to public networks such as the Internet.
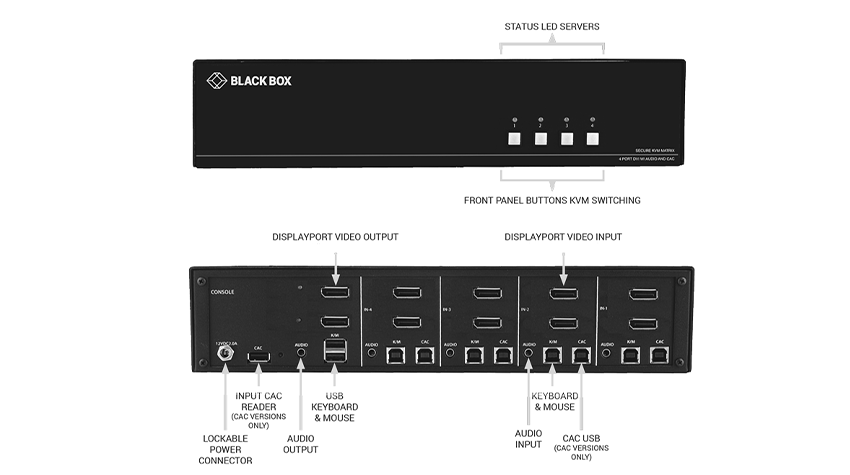
4-Port dual head DisplayPort KVM Switch
Secure KVM Switches
Download BrochureSecure KVM Switches Flyer
Download FlyerSecure KVM Defender NIAP 3.0
Download FlyerImpact and Importance of NIAP PP PSD 4.0
Download WhitepaperClassified Information Kept Classified With Secure KVM
Download WhitepaperSecure KVM: Safeguarding Classified & Secure Information
Watch Webinar