Black Box, a leading ICT Global Solutions Integrator and solutions specialist, is committed to delivering excellence in digital infrastructure solutions. With a strong focus on innovation, expertise, and customer-centricity through tailored Professional & Managed Services, Black Box provides comprehensive and cutting-edge products and solutions tailored to meet the unique needs of its clients.
Our approach at Black Box is best described as "GLOCAL," embodying the philosophy of "Think Global, Act Local." This principle guides us in maintaining strong relationships by providing flexibility to our customers and delivering cost-effective solutions tailored to the specific needs of the countries we operate in.
As a prominent global ICT solutions provider, Black Box is committed to promoting sustainable and responsible business practices. We strive to align our operations with robust sustainability policies, adhere to best practices, and meet high reporting standards. Our ongoing dedication extends to achieving diversity, equity, and inclusion targets within our workplace, ensuring a supportive and inclusive environment for all.
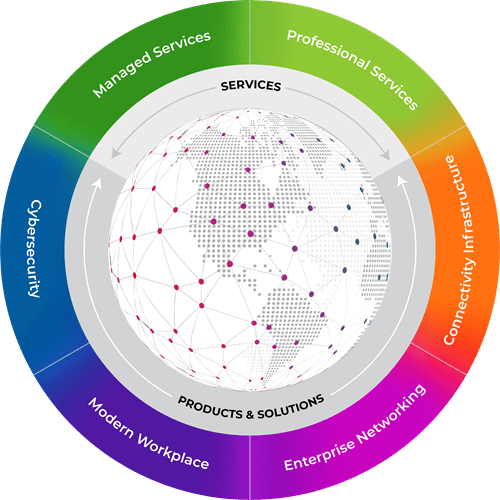
Great customer experiences, exceptional workspaces, and resilient networks all begin with strategic planning and top technical professionals dedicated to delivering solutions and services that help organizations design, build, manage, and secure their IT for future growth.
Spaces need to be interactive, adaptive, and secure. Discover how to enhance security, increase efficiencies, automate operations, and personalize workplace interactions.
Learn MoreAccelerated by the pandemic, skyrocketing demand for processing power is driving the demand for new or expanded data centers.
Learn MoreTransform networks to empower employees to work and collaborate, securely and seamlessly, anywhere on any device — with no disruption.
Learn MoreFaster, better wireless is here now. Develop a strategy that supports everything wireless with mission-critical performance that is built-in from design to deployment and beyond.
Learn MoreWhen you partner with Black Box, you partner with industry leaders. Our vast portfolio includes solutions from our own Black Box Technology Product Solutions business with pro-AV brands such as Radian Flex.
Learn MoreSupporting an omni-channel customer journey has become more complex than ever because of the global remote and hybrid work revolution.
Learn MoreTransform how you interact with the ever-evolving digital world. Fuel productivity, gain cost efficiencies, and scale up business opportunities with IT solutions designed to help you build, manage, optimize, and secure your network.

Work seamlessly together to address all your video infrastructure and AV needs. Deploy digital signage, enhance presentations, and extend video beyond the boardroom.
Read More
Find the right solution for storing, securing, and protecting your IT equipment from a wide variety of cabinets, racks, enclosures and accessories.
Read More
Construct and expand networks of all sizes from small offices to global enterprises to deliver optimized security and unlimited bandwidth.
Read MoreEmpowering your enterprise through cutting-edge technology solutions and world-class consulting services, we place your unique business and industry challenges at the forefront of all we do.
Transportation
Keeping transportation operations safe and on-time comes down to having the right connectivity technology and managed services provided to help you track every issue, delay, and emergency in real time so operators can make instant, informed decisions.
Read MoreRetail
Digitalization continues to shape the interactive, integrated consumer experience. Competition for customers will be won by those who create and integrate a seamless online engagement with an in-store customer experience.
Read MoreMilitary & Defense
When secure, compliant technology solutions are a must, you need advanced products that meet the latest and most rigid security standards to help you achieve your objectives, meet your budget, and optimize your productivity without sacrificing safety.
Read MoreManufacturing
Wired and wireless infrastructures, integrated communications, IoT devices, and managed service solutions bridge the gap between production and transformation — driving agile manufacturing processes, cost-of-quality, and demand flow output.
Read MoreHealthcare
Unlike any other industry, your patients depend on you to be on the cutting edge of technology. Healthcare technology must drive patient care, optimize workflows, improve satisfaction, and streamline operations, all while balancing industry and government regulations.
Read MoreBroadcast
Evolving technology and the rapid transition to cloud-based workflows is driving automated broadcast operations for program transmission, master control, news production, and live production.
Read MoreStaying ahead of the technological curve isn’t easy. Learn from industry experts how modern IT is laying the foundation for rapid adoption and achievable innovation, sustainability, and business resiliency.
When our customers succeed, we succeed, even in the most challenging environments and circumstances. See how our team anticipates the ever-changing needs of our customers and helps them accelerate their success.